Welcome Note from Abhi Thorat, Founder & CEO, Securim
Lessons Learned from 2025
As we step into a new year, January is the perfect moment to pause and reflect on the lessons 2025 reinforced for all of us in cybersecurity and compliance.
Last year made one thing clear: Security maturity is no longer defined by tools alone. Organizations that fared best weren’t necessarily the ones with the largest budgets, but those with clarity — clarity around their data, their risks, and their responsibilities. We saw compliance frameworks continue to evolve, threat actors become faster and more targeted, and regulators place greater emphasis on accountability and evidence.
The most successful security programs in 2025 shared three traits:
• They treated compliance as an operational discipline, not an audit event.
• They invested in people and processes alongside technology.
• They embraced continuous improvement rather than one-time fixes.
At Securim, these lessons continue to shape how we help our clients — building resilient programs that adapt as threats, regulations, and business priorities change. As we move into 2026, our focus remains the same: helping organizations stay proactive, prepared, and confident in the face of uncertainty.
Welcome to the January issue of Your Cyber & Compliance Compass.
Subscribe to Your Cyber & Compliance Compass
Community Engagement: Firland Foundation & Workshop Tour
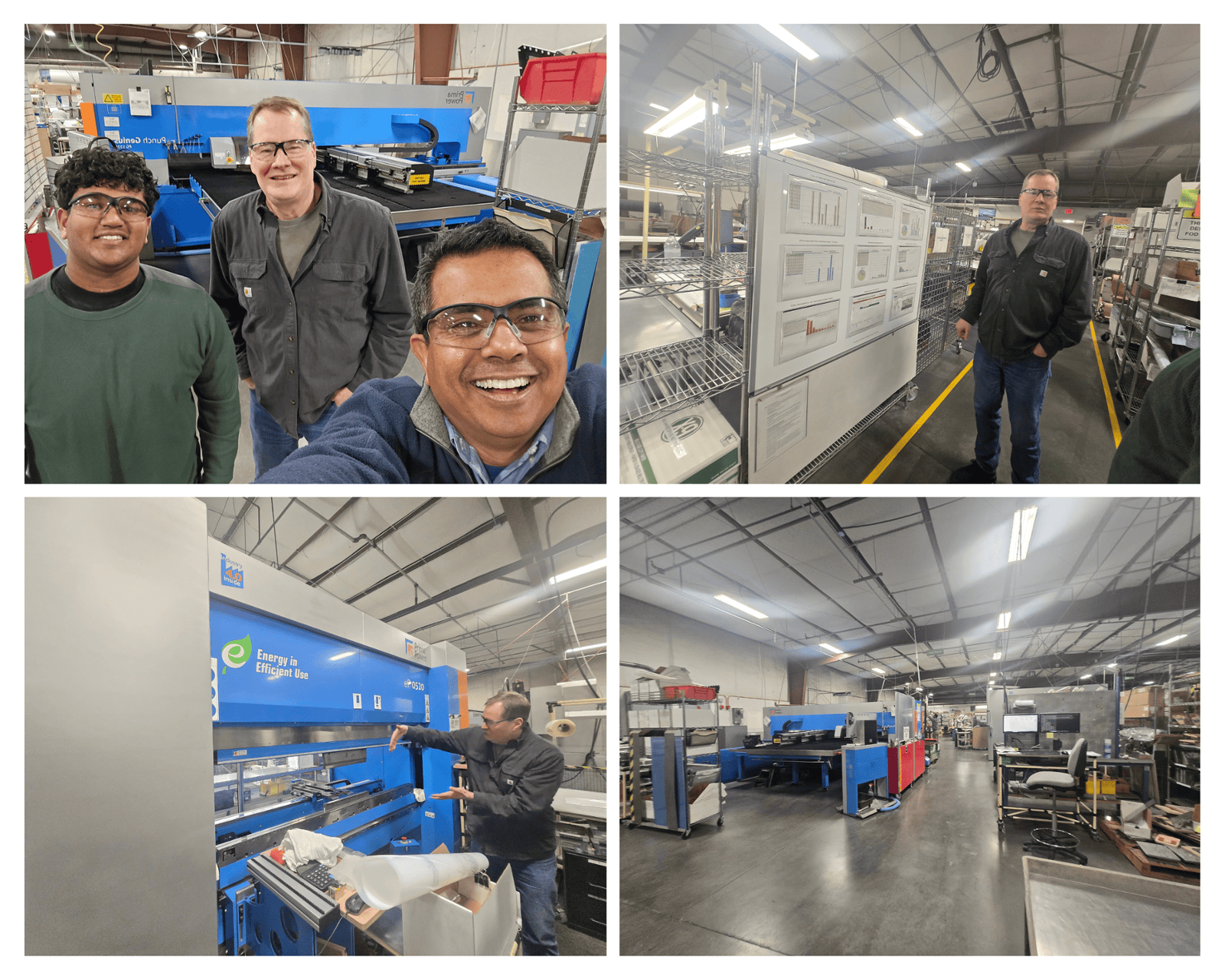
This month, we had the opportunity to visit the Firland Foundation and tour its Community Manufacturing Program in Shoreline. Firland is a fellow member of the Pacific Northwest Defense Coalition (PNDC) and plays an important role in strengthening both the manufacturing ecosystem and the broader community.
The visit offered a firsthand look at how Firland combines disciplined aerospace manufacturing practices with a strong commitment to workforce development. Their program emphasizes continuous improvement through a Kaizen mindset, while creating meaningful employment pathways for individuals facing barriers to traditional employment.
What stood out most was the balance Firland strikes between operational rigor and human impact. From close collaboration with industry partners to a culture that values skill-building and long-term opportunity, Firland demonstrates how manufacturing excellence and community mission can reinforce one another.
We’re grateful for the opportunity to learn from Firland’s work and look forward to staying engaged with organizations that strengthen the manufacturing community through purpose-driven leadership.
Learn more about Firland Foundation and their work below:
Cybersecurity in 2026: What Leaders Should Be Planning for Now
As organizations move into 2026, cybersecurity is no longer just an IT concern — it’s a business resilience issue that touches operations, compliance, and leadership decision-making. Based on what we observed across public sector, healthcare, and regulated industries in 2025, three priorities are emerging as critical for the year ahead:
1. Continuous Compliance Over Point-in-Time Audits
Regulators and customers alike are shifting expectations. Annual assessments are no longer enough. Organizations are expected to demonstrate ongoing control effectiveness, real evidence, and operational maturity — especially for frameworks like CMMC, HIPAA, and SOC 2.
2. Security Readiness for Third-Party and Supply Chain Risk
Vendors, subcontractors, and partners remain one of the most common attack paths. In 2026, we expect increased scrutiny around vendor risk management, contractual security requirements, and documented oversight.
3. Executive Accountability for Cyber Risk
Cybersecurity decisions are increasingly landing at the leadership and board level. Clear risk ownership, documented decision-making, and alignment between business objectives and security investments will separate reactive programs from resilient ones.
How to Get Ahead This Year
• Conduct a gap assessment aligned to your most relevant framework
• Validate incident response readiness with tabletop exercises
• Ensure leadership visibility into cyber risk and compliance posture
Organizations that plan early — rather than react late — will be better positioned to meet regulatory demands, customer expectations, and evolving threat realities in 2026.
Organization Spotlight: Washington Learning Source
Learn more: https://www.walearningsource.org/

Framework Focus: CMMC — Strengthening the Defense Supply Chain
For organizations working with the Department of Defense or participating in the defense supply chain, Cybersecurity Maturity Model Certification (CMMC) remains a critical requirement — and a growing priority in 2026.
CMMC is designed to ensure contractors protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) through consistent, verifiable cybersecurity practices. Unlike self-attestation models of the past, CMMC emphasizes accountability, evidence, and sustained implementation.
At its core, CMMC is about reducing risk across the defense industrial base. Threat actors increasingly target smaller suppliers, knowing that a single weak link can compromise an entire ecosystem.
Key focus areas include:
• Access control and identity management
• Incident response and reporting
• Configuration and vulnerability management
• Security awareness and training
• Documentation and policy enforcement
CMMC 2.0 places renewed emphasis on aligning security controls with real-world risk and operational maturity, not just compliance checklists.
Getting started with CMMC:
Identify whether you handle FCI or CUI.
Assess your current posture against required practices.
Build a roadmap that prioritizes gaps, evidence, and sustainability.
CMMC compliance isn’t just about eligibility — it’s about trust, resilience, and long-term participation in the defense supply chain.
Learn more: https://www.securim.com/cmmc-framework
Closing Note
Upcoming Cybersecurity and Compliance Events
Webinar: World Cup Ready - Mastering Inventory for Mega Events
January 28, 11:00 AM - 12:00 PM (Virtual)
Why this matters: Learn how to prepare inventory, operations, and risk management for global events.
PNAA Advance 2026: Celebrating 25 Years of Community
February 9-11, Lynwood, WA
Why this matters: A valuable opportunity to connect with regional business leaders, partners, and chamber members across industries.
ISACA Puget Sound Chapter Meeting: FedRamp: How it's changing, the good and the bad
February 10, 12:00 - 1:00 PM,
(Virtual)
Why this matters: Come together to share knowledge, build partnerships, and shape a stronger, more resilient aerospace future.
PNDC - Supply Chain Opportunities Conference (SCOC)
February 26, 8:30 AM - 2:30 PM PST, Clackamas, OR
Why this matters: Connect with peers to strengthen local supply chains and partnerships across the Pacific NW.

